IoT Security Tips to Protect Your Small Business by Drew Robb. Available from<http://www.smallbusinesscomputing.com/tipsforsmallbusiness/iot-security-tips-to-protect-your-small-business.html> [Posted November 07, 2016]
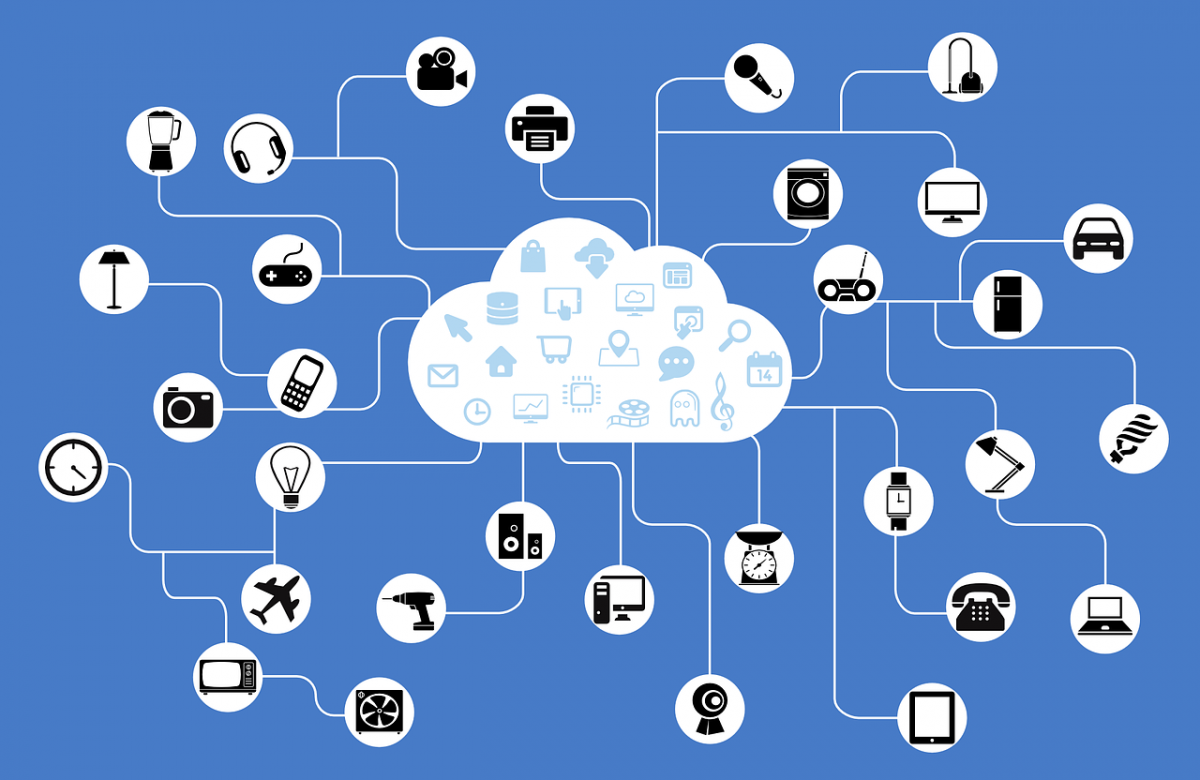
This article examines the recent Internet of Things (IoT) attacks and offers expert tips on how to secure IoT devices.
Last month on October 21, millions of people could not connect to websites like Twitter, Netflix, Spotify, Airbnb, Reddit, Etsy, SoundCloud and The New York Times—due to what’s known as a distributed denial-of-service (DDoS) attack. The culprit? Tens of thousands of Internet of Things (IoT) devices that contain wireless sensors to connect to the Internet. Hackers compromised cameras, coffee makers, web cams, DVRs, surveillance cameras, routers, anything they could get their hands on. And they used these devices—without their owners knowing—to unleash a flood of overwhelming Internet traffic that took down all these sites.
“The latest DDoS attack used connected devices such as smart refrigerators and thermostats,” said Frank Scavo, president of Computer Economics. “They flooded the network with a large number of transactions, until these websites were unable to process legitimate transactions.”
Understanding the Need for IoT Security
The IoT is the subject of tremendous hype of late. Analyst firm Gartner predicts that by 2020, more than twenty billion devices will be connected to networks worldwide. The vision behind this includes: smart traffic lights that don’t leave you idling at a junction for several minutes when nothing is coming the other way; coffee makers networked to the front door or to your phone so coffee is ready and waiting upon your arrival; and fridges that send reminders to order grocery items in short supply.
The problem is that every wireless sensor and each networked device represents a possible entry point for an attacker. And if hackers can use them to bring down the Web, how difficult do you think it will be to use them to infiltrate a small business network?
Unfortunately, most of these IoT devices contain little in the way of security features. If even when they do, they’re neglected. People never change the factory set password—such as 0000 or 1234—when they are installed, so millions of devices end up with the same easy-to-hack password.
For example, a security conference called Black Hat Europe recently discovered a security vulnerability between IoT devices and Android phones. Belkin home automation devices—such as electrical switches, cameras, light bulbs, coffee makers, and air purifiers—could be used access the phones that program and control the devices.
“Hackers can use the IoT device to hop right into the network,” said Chris Coleman, senior engineering manager at VeeDog, a small business ransomware-prevention vendor. “Anyone using such devices in a small business could find their servers suddenly overcome by malware.”
He said that wireless Internet routers in small businesses are particularly prone to attack if they’re not well protected. But there are also known cases of business cell phones being hacked via the office coffee maker.
“A lot of devices out there have intelligent connections to the Internet that represent a real and persistent danger to your business,” said Coleman.
IoT Security Tips
We spoke to security industry experts who offered their best IoT security tips to help you prevent your business from falling victim to an IoT attack. Here’s what they had to say:
- Software Updates: Keep the software for your computer network, servers, laptops, desktops, network switches, wireless routers, and any other devices up-to-date, particularly with the latest manufacturer security updates.
- Strong Passwords: Never use default passwords for devices once you set them up. Change them and keep them secure. This means no sloppy password construction: like using your name, the actual word “password,” or other easy-to-hack terms. Remove Post-It notes stuck on screens or cubicles that serve as password reminders.
- Wireless Security: Wireless devices use certain security methods, and some are easier to hack than others. Coleman recommends disabling Wi-Fi Protected Setup (WPS) and using only Wi-Fi Protected Access 2 (WPA2).
- Home Security: Make sure that you and your employees take safe practices home, especially if any of you conduct business from home. The bad guys like to comprise home computers. They find the ones that connect to business networks, capture passwords, and quietly move into the business. From there, they can wreak havoc.
“Hackers rely on security ignorance, and they take advantage of your business by mining for choice nuggets [e.g., data, usernames, passwords] in home computers,” said Coleman.
- Data Backups: Invest in a data backup strategy, and make sure that you or designated IT person/team—knows how to restore your data in the event of disaster. If you lose a computer or a server that’s critical to your company survival, proper backup and restore procedures will help you turn a potential disaster into a mere nuisance.
- Get IT Help: Hackers rely on ignorance. If you have an IT person in your business, hold her responsible for security and encourage her to gain expertise—fast. If you have enough personnel, appoint someone to solely look after IT security and justify it by the fact that the bad guys are hitting everyone right now. If you don’t have enough staff or in-house expertise, hire outside help to handle that responsibility.
“Network consulting firms, security consulting firms, and managed service providers will assess your network, your website, and any connected devices that you have,” said Scavo. “They can help you decide what security measures you need to take to protect your company.”
- DDoS Protection: If your website lies at the heart of your business, and it makes you a lot of money, consider securing additional protection against a Distributed Denial of Service attack. Attackers can either target you directly or you may just get caught in the crossfire when they go after your Internet Service Provider (ISP).
“If you want to be sure you website cannot be shut down by a DDoS attack, your website needs to be hosted by special Internet hosting companies that specialize in DDoS mitigation,” said Stu Sjouwerman, CEO of security awareness training vendor KnowBe4. There is an industry that does this, but it’s not cheap. If you can’t afford it, call your ISP and ask how they mitigate against DDoS attacks. Find the ISP that has the best measures in place.
- Credit Cards: Small business owners have complained about being forced to buy the latest credit card payment machines that include a chip reader. But the Smart Card Alliance believes this adds another layer of protection against hackers. Every IoT device serves as a potential entry point onto the network, and that includes credit card machines and bank accounts.
“These recent DDoS attacks, one of which was more than four times the size of the largest reported attack last year, are comparable to the massive payments data breaches that have been in the spotlight over the past few years,” said Randy Vanderhoof, executive director of the Smart Card Alliance. “This is just the latest example of the IoT vulnerabilities that exist today, and it demonstrates why IoT security is so critical.”
- Physical Security: Amir Sharif, co-founder and vice-president of business of Aporeto, a cloud security company, pointed out that even with all of the above safeguards in place and with top-of-the-line security practices in force, a business could still become a victim due to one insecure IoT point.
Hackers could use an innocuous device sitting in the corner to unlock a company’s physical doors remotely. They could then send in a local person to install sophisticated snooping devices that map keyboard strokes, record voice data, steal video streams off of computers, and so forth. With that information they can silently siphoned bank accounts over a long period with what would appear to be a series of legitimate transactions. “Buy IoT devices only if you have a good business need for them,” said Sharif. “Buy devices from well-known companies that stand behind their product and provide some indemnity.”
- Video Cameras:Surveillance technology has become incredibly affordable, and it’s been deployed by many small businesses. Increasingly these devices can connect to the Internet, and that poses a threat. “You should keep Internet-enabled devices—like video cameras—on a separate network from the primary business network that deals with customer financial transactions, like point of sale systems, intellectual property, or any form of regulated data,” said Chris Morales, head of security analytics at Vectra Networks.
Mat Gangwer, chief technology officer at Rook Security, takes this a step further. He advises small businesses to keep all IoT devices off the corporate network except those that are absolutely needed. “It doesn’t require a huge IT budget to make an organization a little more secure, to make it a more difficult target,” said Gangwer. “Most hackers go after the really the easy targets.”
- Security Technology: Of course, small businesses still need the usual security technologies place: anti-virus, anti-malware, firewalls, encryption and, especially these days, ransomware protection. VeeDog, for example, is designed for small businesses. It monitors the network data flow, flags suspicious files, and analyzes them for destructive or malicious intention. It disables any file verified as malware, and then it submits the malware file to the customer’s anti-virus provider so that it can distribute a fix to all their customers.
- Educate Employees:Most breaches, hacks, and ransomware result from human error; someone somewhere within the organization got sloppy or lacked proper security education—or both. And it’s shocking how easy it is to trick employees. One company hired an outside organization to pretend to be its IT department. It sent employees emails asking for their user passwords. Out of 200 employees, 113 their passwords immediately.
Opening email attachments or links from unknown or unverified senders is a poor practice, yet it remains an easy, viable way to gain unauthorized entry. Employees need training on how to spot suspicious emails.
How can you tell if the email is NOT from your bank or from the IT department? Hover your cursor over the name shown as the sender. Hackers can make something look like a legit email yet when you put the cursor there, the actual email address shows up as something along the lines as nasty.hacker@aol.com.
Security experts agree that ransomware attacks will only increase, which makes security awareness training a sensible defense. Employees learn the various tricks of the hacking and ransomware trade so they don’t get conned. Training programs also send out spoof email links to see how many employees click on them. They track the percentage, and the training helps to reduce the number over time. It’s shocking how many people, including bosses, get fooled.
Don’t Let IoT Fear Paralyze Your Business
Yes, our highly connected world can seem much too scary. One in 40 small businesses is at risk of a cyberattack, according to a Symantec report. This translates directly into dollars lost—the National Small Business Association found that, on average, cyberattacks cost small businesses more than $7,000.
“Businesses that have connected devices, such as smart-factory or smart-warehouse equipment, need to be aware of the threat and to make sure their devices have security protection,” said Scavo. “Otherwise criminals could take down your factory or your warehouse and demand ransom to get it back up and running.”
Such possibilities could cause some business people to yearn for the good old days when they never had to worry about hackers and malware. But it’s really not much different than moving from a tiny community where no one locks their doors to large city—where you have to change your habits and take sensible precautions.
“The risk is relatively small if a business takes basic steps to protect its network,” said Mike Bergman, senior director of technology and standards at the Consumer Technology Association.
Mankind successfully made the transition from a lower-crime agrarian existence into a higher-crime industrial world. The same can be done with the Internet of Things. Just as the benefits of industry were found to outweigh the many drawbacks, so it is with a more connected world.
“At the end of the day, we’ll see that the benefits IoT provides to the small business owners outweigh the cost,” said Sharif. “Life will go on.”
IoT Security Tips to Protect Your Small Business by Drew Robb. Available from<http://www.smallbusinesscomputing.com/tipsforsmallbusiness/iot-security-tips-to-protect-your-small-business.html> [Posted November 07, 2016]